TL;DR (Teamwire users): A vulnerability has been found in Teamwire which can allow malicious users to execute commands on victim’s computers by sending a crafted Teamwire message. Upgrade Teamwire to the newest version as soon as possible to fix this vulnerability.
TL;DR (Technical): Template injections are a common vulnerability in web applications. If a desktop application built on a web engine is vulnerable to template injection, this can result in remote code execution on the client system.
Background
Template injection refers to a class of vulnerabilities that exploit the insecure embedding of user controllable data into template engines like AngularJS. Template engines use template files to define the design of a user interface by inserting special placeholders into a text. The template engine then dynamically replaces the placeholders with data at runtime, referred to as “rendering” the template. Many modern template engines even support carrying out complex computations inside the templates themselves. If an attacker embed one of these placeholders into a template, he can often execute functions in the underlying programming language.
To help support cross-platform compatibility, software vendors started embedding web engines into client desktop applications, thus removing the need to develop native applications for all different client platforms. NW.js is a technology that combines the browser engine WebKit with the JavaScript framework Node.js, and is often used to create cross-platform applications. This combination enables users to call Node.js functions directly from the DOM of the embedded Chromium browser.
For web applications, template injections are well known problem. Due to the increasing use of web technologies for the rapid development of client applications, this class of vulnerabilities has begun to manifest itself on the desktop too.
Teamwire is a “fast, intuitive and secure enterprise messaging app” for businesses. Teamwire clients are available for iPhone, iPad, Android, Windows Phone, Windows PC, Mac OS and Linux.
HiSolutions researchers have found two distinct template injection vulnerabilities during an internal security assessment of the Teamwire messaging platform (clients on Windows and the administrative interface), which could be used to target end users or platform administrators.
Technical Background
Teamwire is built on AngularJS. Angular implements a secure sandbox to attempt to prevent attacks even if user input is insecurely embedded in templates. As the sandbox was repeatedly bypassed, AngularJS developers decided that the effort was futile and shifted the responsibility back to application developers. Currently, bypasses exist for all AngularJS Versions that enable an attacker to escape from the sandbox and execute arbitrary JavaScript commands.
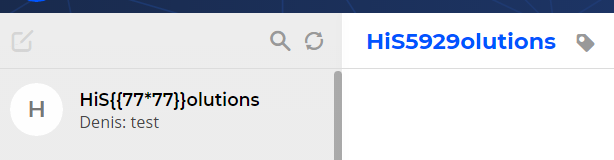
Template injections in AngularJS can be illustrated as follows: If an attacker succeeds in inserting placeholder string, delineated with double curly brackets ( “{{…}}” ) into a template inside the application, any operations inside the brackets will be carried out when the template is rendered. In this case, inserting {{77*77}} into the name field (left) results in the product (5929) being displayed in the rendered display (right).
To bypass the sandbox in AngularJS 1.6.8, which is used by Teamwire, the following template string can be used:
{{constructor.constructor(‚###JavaScript-Code-Here###‘)()}}
Vulnerability Details
Stored XXS in Admin Web Interface – CVE-2018-17560
Users can change their displayed usernames in the Teamwire clients without any restrictions. A user could therefore change his username to include a template string:
his {{constructor.constructor(‚document.body.style.backgroundColor = „green“;‘)()}}
Our researchers found that when an administrator views the user inside the administrative web panel, the username is embedded insecurely (i.e. without encoding the placeholder to prevent execution) into the web page and the JavaScript code in the string is executed.
The example payload above only changes the background color of the HTML page, but a malicious user could insert arbitrary JavaScript code to be executed in the browser. An attacker could for example try to take over an administrator’s session or try to execute actions with admin rights in the web portal.
Attempting to delete the “malicious” user also triggers the vulnerability, as the admin must first view the user in the web interface to be able to delete them.
Desktop Client RCE – CVE-2018-17170
Another template injection was found inside the Teamwire desktop client. The vulnerable field was the name of a group chat. A malicious user must first create a chat with a crafted name including the template string. They can exploit this vulnerability to execute code on the victim’s system. If another user included in the chat writes a message to the attacker by selecting him from his contact list, the client merges the chats and the payload is executed on the victim’s system. Because the victim selects the other user from the contact list, he cannot see the manipulated chat name before the JavaScript is executed.
That only the first character of the chat names is displayed in the overview further helps to hide malicious payloads.
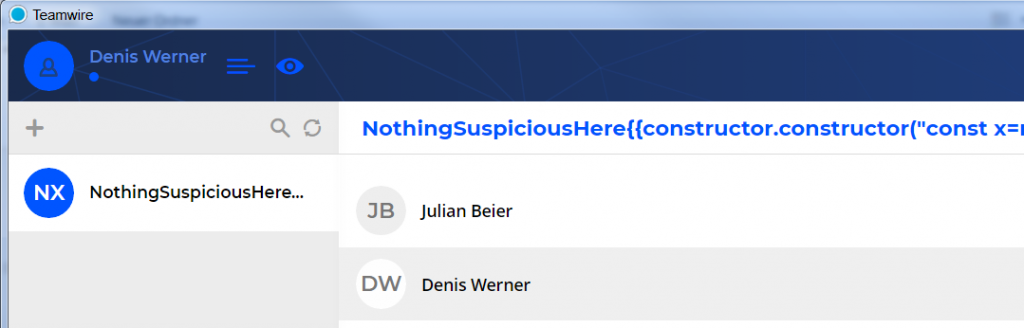
Only the first part of the chat name is shown (left), hiding the malicious part.
The same code execution vulnerability is exploitable when the victim starts a chat with another user with a specially crafted username.
Because the Teamwire desktop client uses NW.js and the embedded Node.js has the ability to spawn arbitrary processes, template injection actually results in remote code execution on the client system.
This example payload opens the windows calculator on the client system:
{{constructor.constructor(„const x=require(‚child_process‘).spawn; x(‚calc.exe‘);“)()}}
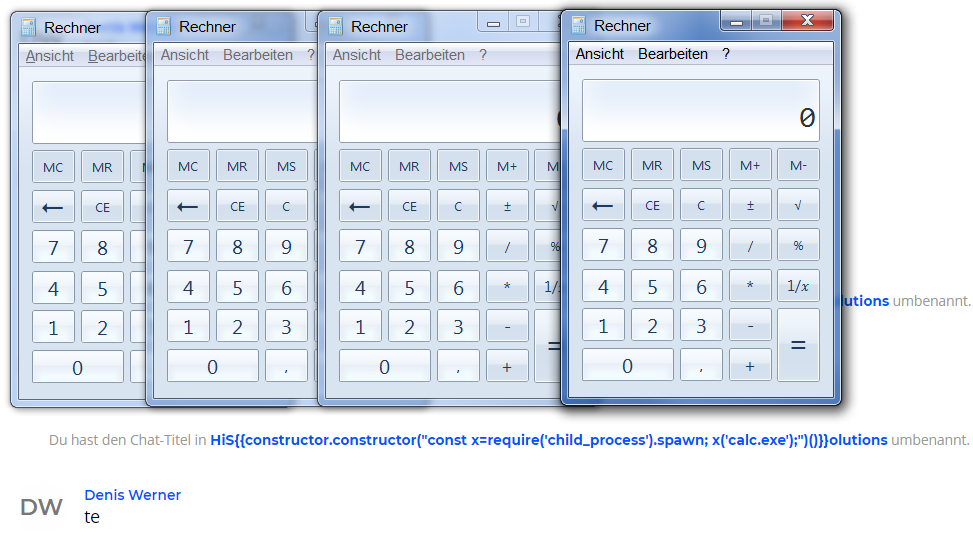
Due to the internal structure of the code, the payload is executed four times when the vulnerability is triggered by sending a message.
Impact and Mitigations
The impact of the vulnerabilities is limited by the fact that a valid user account attributed to the organization is needed to perform the attack. If an attacker has obtained access to an account, no mitigation against the attack in the web interface (apart from not using it) exist. Preventing the code execution attack against the clients requires not accepting any messages from other accounts, obviating the purpose of a messaging application.
The vulnerabilities described above have been fixed in the backend version prod-2018-11-13-15-00-42 and in the desktop client version 1.9.0 released on 16.11.2018. To fully mitigate the vulnerabilities and continue the use of the product, these updates should be installed as soon as possible.
The vulnerability CVE-2018-17170 has been verified for the desktop client version 1.5.1, it affects most likely all versions prio to 1.9.0. The vulnerability CVE-2018-17560 affects all backend version prior to prod-2018-11-13-15-00-42.
Disclosure Timeline
16. October 2018 – Initial contact with the vendor
16. October 2018 – Submission of vulnerability details to the vendor
22. October 2018 – Further communication with vendor
16. November 2018 – Update released
21. June 2019 – Public disclosure (the vendor asked for a postponed publication of the details, which we agreed on)
Credits
The vulnerabiliy was found by Julian Beier, Lars Burhop, Benjamin Braun, Viktor Schlüter and Denis Werner (HiSolutions).


Ein Gedanke zu „Web vulnerabilities are coming to the Desktop – Template Injections lead to RCE in Teamwire“
Die Kommentare sind geschlossen.