During an investigation, HiSolutions discovered a credential leak of a password manager that was installed as browser extension. After reporting the vulnerability, the vendor was quick to respond and implemented a fix.
Summary
The DualSafe Password Manager by iTop before version 1.4.24 leaks credentials as plaintext in a log file that can be accessed by the local user without knowledge of the master secret (CWE-532). This vulnerability was assigned CVE-2024-24272.
Update to the newest version (at least 1.4.24) as soon as possible and replace potentially leaked credentials.
Vulnerability Details
The following details were produced in a test setup with the vulnerable version 1.4.21 of the DualSafe Password Manager installed in Chrome. After storing and using several credential pairs via the blue extension icon on the top right corner, the log file started showing some entries that contain the plaintext credentials.
Logging is done via a text file in the directory of the browser extension, in this case: C:\Users\User\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\lgbjhdkjmpgjgcbcdlhkokkckpjmedgc\000003.log (file name may vary).
The following image depicts the credential pair stored in DualSafe (right) as well as the log file that contains the same password as plaintext (left).
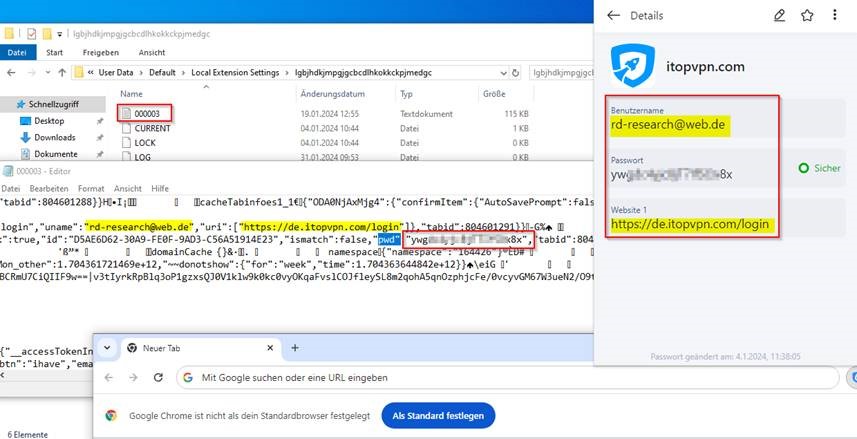
One interesting thing to note is that, while the log file contains some credentials as plaintext in a structure like this one: cacheTabinfoes1_1Þ{"[...]":{"confirmItem":{"pwd":"<password>",[...], "type":"login","uname":"<user>","uri":["<url>"]}}}, there are also similar structures with the key pwd but their value is encrypted. Though the observed log events did not indicate the exact trigger for an entry with a plaintext password, passwords could already be extracted after just a few login attempts.
Usually, the password manager requires a master secret to unlock and access the stored credentials. This vulnerability allows an attacker to harvest stored credentials from the log file without knowing the master secret.
Remediation
iTop announced a fix in version 1.4.24.
Shortly after reporting the vulnerability details to iTop, a fix was implemented and rolled out across Firefox, Edge, and Chrome. Update to the newest version as soon as possible and check for potentially leaked passwords in the described location (the exact path depends on the browser).
Should passwords have been leaked this way, rotate them after updating the extension.
Responsible Disclosure Timeline
- 04.01.2024 – HiSolutions contacts iTop
- 30.01.2024 – HiSolutions contacts iTop again after no response
- 31.01.2024 – iTop responds and requests vulnerability details
- 31.01.2024 – HiSolutions provides all vulnerability details
- 01.02.2024 – iTop announces that a fix has been implemented and will be published soon
- 02.02.2024 – iTop requests a delay before publication to roll out the fix
- 05.02.2024 – iTop releases 1.4.24 on Firefox and Edge
- 15.02.2024 – iTop releases 1.4.24 on Chrome
- 12.03.2024 – HiSolution requests green light for publication
- 13.03.2024 – iTop accepts and states that 1.4.24 fixes the vulnerability
Credits
This vulnerability was discovered by Paula T., Joshua Z. and Pascal B. (HiSolutions AG). We also thank iTop for their swift response and remediation regarding this vulnerability.
